Arcitura Education S90.20 Exam - Topic 1 Question 27 Discussion
Topic #: 1
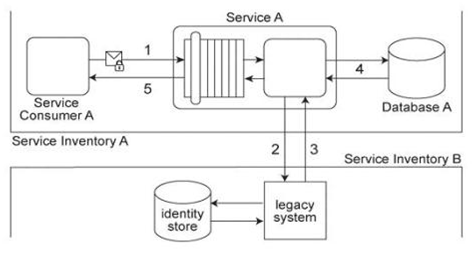
Service Consumer A submits a request message with security credentials to Service A (1). The identity store that Service A needs to use in order to authenticate the security credentials can only be accessed via a legacy system that resides in a different service inventory. Therefore, to authenticate Service Consumer A, Service A must first forward the security credentials to the legacy system (2). The legacy system then returns the requested identity to Service A (3). Service A authenticates Service Consumer A against the identity received from the legacy system. If the authentication is successful, Service A retrieves the requested data from Database A (4), and returns the data in a response message sent back to Service Consumer A (5). Service A belongs to Service Inventory A which further belongs to Security Domain A and the legacy system belongs to Service Inventory B which further belongs to Security Domain B .(The legacy system is encapsulated by other services within Service Inventory B, which are not shown in the diagram.) These two security domains trust each other. Communication between Service A and the legacy system is kept confidential using transport-layer security. No intermediary service agents currently exist between the two service inventories. However, it has been announced that due to the introduction of new systems, some intermediary service agents may be implemented in the near future. Additionally, the legacy system has been scheduled for retirement and will be replaced by a new identity management system that will provide a new identity store. Because the new identity store will need to serve many different systems, there are concerns that it could become a performance bottleneck. As a result, services (including Service A and other services in Security Domains A and B) will not be allowed to directly access the new identity store. Which of the following statements describes a solution that can accommodate the requirements of the new identity store, the authentication requirements of Service A, and can further ensure that message exchanges between Security Domains A and B remain confidential after intermediary service agents are introduced?
Blondell
5 months agoChanel
6 months agoMartina
6 months agoBerry
6 months agoFranchesca
6 months agoMica
6 months agoAudry
6 months agoAdela
6 months agoSalley
6 months agoTamar
7 months agoPearly
7 months ago