Arcitura Education S90.20 Exam - Topic 1 Question 24 Discussion
Topic #: 1
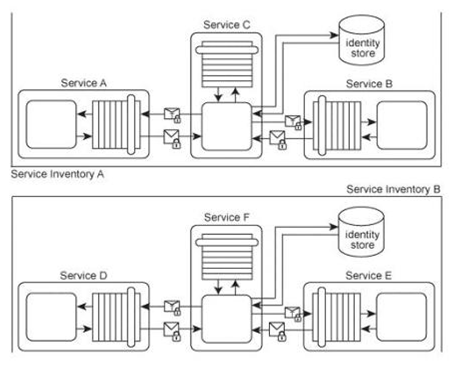
Services A, B and C belong to Service Inventory A .Services D, E and F belong to Service Inventory B .Service C acts as an authentication broker for Service Inventory A .Service F acts as an authentication broker for Service Inventory B .Both of the authentication brokers use Kerberos-based authentication technologies. Upon receiving a request message from a service consumer, Services C and F authenticate the request using a local identity store and then use a separate Ticket Granting Service (not shown) to issue the Kerberos ticket to the service consumer. A recent security audit of the two service inventories revealed that both authentication brokers have been victims of attacks. In Service Inventory A, the attacker has been intercepting and modifying the credential information sent by Service C (the ticket requester) to the Ticket Granting Service. As a result, the requests have been invalidated and incorrectly rejected by the Ticket Granting Service. In Service Inventory B, the attacker has been obtaining service consumer credentials and has used them to request and receive valid tickets from the Ticket Granting Service. The attacker has then used these tickets to enable malicious service consumers to gain access to other services within the service inventory. How can the two service inventory security architectures be improved in order to counter these attacks?
Lynelle
6 months agoPage
6 months agoLilli
6 months agoShala
6 months agoPhillip
6 months agoOna
7 months agoJulene
7 months agoRusty
7 months agoArlette
7 months agoWillow
7 months agoSabra
7 months ago