Arcitura Education S90.20 Exam - Topic 1 Question 18 Discussion
Topic #: 1
Service Consumer A sends a request message to Service A (1) after which Service A retrieves financial data from Database A (2). Service A then sends a request message with the retrieved data to Service B (3). Service B exchanges messages with Service C (4) and Service D (5), which perform a series of calculations on the data and return the results to Service A .Service A uses these results to update Database A (7) and finally sends a response message to Service Consumer A (8). Component B has direct, independent access to Database A and is fully trusted by Database A .Both Component B and Database A reside within Organization A .Service Consumer A and Services A, B, C, and D are external to the organizational boundary of Organization A .
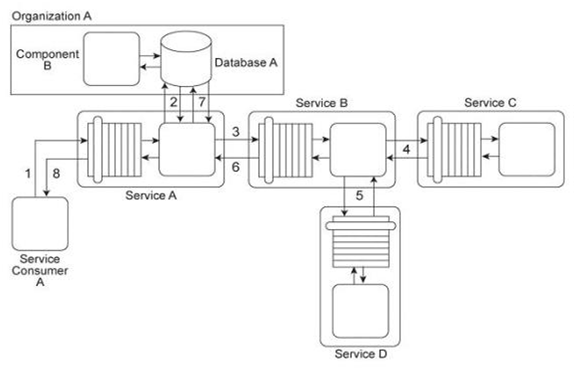
Component B is considered a mission critical program that requires guaranteed access to and fast response from Database A .Service A was recently the victim of a denial of service attack, which resulted in Database A becoming unavailable for extended periods of time (which further compromised Component B). Additionally, Services B, C, and D have repeatedly been victims of malicious intermediary attacks, which have further destabilized the performance of Service A .How can this architecture be improved to prevent these attacks?
Tammara
6 months agoDorothy
6 months agoIraida
6 months agoBarney
6 months agoAzzie
6 months agoGeorgeanna
7 months agoBrice
7 months agoLanie
7 months agoCristal
7 months agoSalome
7 months ago