Arcitura Education S90.20 Exam - Topic 1 Question 16 Discussion
Topic #: 1
Service Consumer A sends a request message to Service A (1), after which Service A sends a request message with security credentials to Service B (2). Service B authenticates the request and, if the authentication is successful, writes data from the request message into Database B (3). Service B then sends a request message to Service C (4), which is not required to issue a response message. Service B then sends a response message back to Service A (5). After processing Service B's response, Service A sends another request message with security credentials to Service B (6). After successfully authenticating this second request message from Service A, Service B sends a request message to Service D (7). Service D is also not required to issue a response message. Finally, Service B sends a response message to Service A (8), after which Service A records the response message contents in Database A (9) before sending its own response message to Service Consumer A (10).
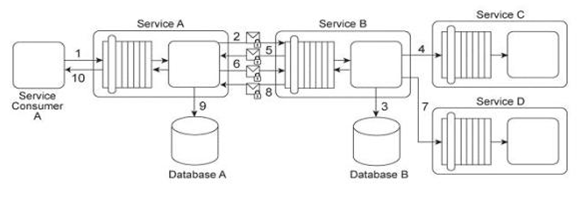
Services A and B use digital certificates to support message integrity and authentication. With every message exchange between the two services (2, 5, 6, 8), the digital certificates are used. It has been determined that both Databases A and B are vulnerable to malicious attackers that may try to directly access sensitive data records. Furthermore, performance logs have revealed that the current exchange of digital certificates between Services A and B is unacceptably slow. How can the integrity and authenticity of messages exchanged between Services A and B be maintained, but with improved runtime performance - and - how can Databases A and B be protected with minimal additional impact on performance?
Fredric
6 months agoTijuana
6 months agoKrissy
6 months agoCiara
6 months agoBrendan
6 months agoSuzi
7 months agoPamella
7 months ago