Arcitura Education S90.20 Exam - Topic 1 Question 15 Discussion
Topic #: 1
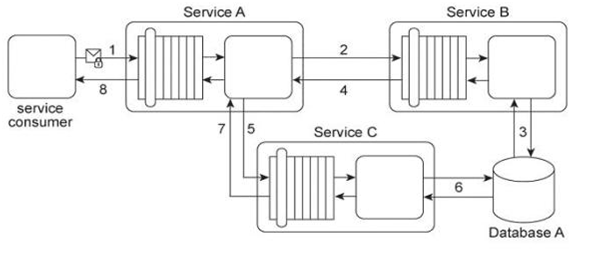
Service A provides a customized report generating capability. Due to infrastructure limitations, the number of service consumers permitted to access Service A concurrently is strictly controlled. Service A validates request messages based on the supplied credentials (1). If the authentication of the request message is successful, Service A sends a message to Service B (2) to retrieve the required data from Database A (3). Service A stores the response from Service B (4) in memory and then issues a request message to Service C (5). Service C retrieves a different set of data from Database A (6) and sends the result back to Service A (7). Service A consolidates the data received from Services B and C and sends the generated report in the response message to its service consumer (8).
This service composition was recently shut down after it was discovered that Database A had been successfully attacked twice in a row. The first type of attack consisted of a series of coordinated request messages sent by the same malicious service consumer, with the intention of triggering a range of exception conditions within the database in order to generate various error messages. The second type of attack consisted of a service consumer sending request messages with malicious input with the intention of gaining control over the database server. This attack resulted in the deletion of database records and tables. An investigation revealed that both attacks were carried out by malicious service consumers that were authorized. How can the service composition security architecture be improved to prevent these types of attacks?
Hubert
6 months agoMeghan
6 months agoArmando
6 months agoLavelle
6 months agoMalcom
6 months agoSamira
7 months agoFairy
7 months agoNoel
7 months ago