Arcitura Education S90.20 Exam - Topic 1 Question 10 Discussion
Topic #: 1
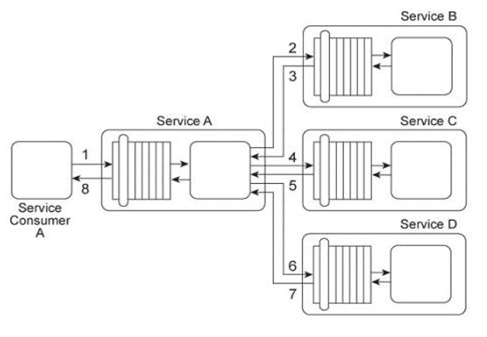
Service A provides a data retrieval capability that can be used by a range of service consumers, including Service Consumer A .In order to retrieve the necessary data, Service Consumer A first sends a request message to Service A (1). Service A then exchanges request and response messages with Service B (2, 3), Service C (4, 5), and Service D (6. 7). After receiving all three response messages from Services B .C .and D, Service A assembles the collected data into a response message that it returns to Service Consumer A (8). The owner of Service A charges service consumers for each usage of the data retrieval capability. Recently, the owner of Service Consumer A has complained that the data returned by Service A is incorrect, incomplete, and from invalid sources. As evidence, the Service Consumer A owner has presented the owner of Service A with sample messages containing the incorrect and incomplete contents. As a result, the Service Consumer A owner has refused to pay the usage fees. Subsequent to an internal investigation, the owner of Service A determines that the data returned by Service A is consistently correct and complete. There are suspicions that the Service Consumer A owner is altering the original messages and issuing these complaints fraudulently in order to avoid paying the usage fees. How can the owner of Service A prove that Service A is returning correct and complete data and that this data originated from the correct sources?
Aracelis
6 months agoGennie
6 months agoJames
6 months agoRyan
6 months agoBrittni
6 months agoLashaunda
7 months agoDominga
7 months agoShelia
7 months agoLachelle
7 months agoAvery
7 months ago