Arcitura Education C90.06 Exam - Topic 1 Question 1 Discussion
Topic #: 1
Virtual Server A and Virtual Server B are hosted by Hypervisor A, which resides on Physical Server A. Virtual Server A hosts Cloud Service A. Virtual Server C. Virtual Server D, Virtual Server E and Virtual Server F are hosted by Hypervisor B on Physical Server B. Physical Server C, which hosts Hypervisor C, is currently not being used.
Cloud Service Consumer A accesses Cloud Service A (1), which accesses files stored in a folder on Virtual Server A (2). Cloud Consumer B uses Proprietary User Portal A to administer legacy software (not shown) installed on Virtual Server D (3). Proprietary User Portal B and Proprietary User Portal C are also available for accessing additional legacy systems located on Virtual Server F; however, they are not often used.
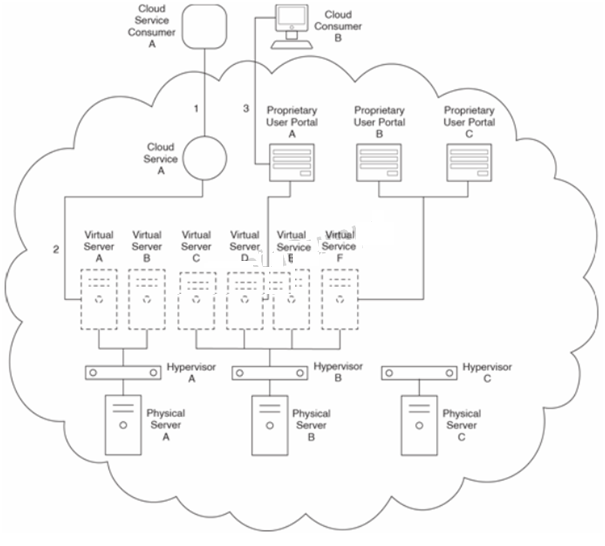
The cloud shown in the figure is a private cloud. Department A and Department B share IT resources within the private cloud and are part of the same organization. Cloud Service Consumer A belongs to Department A and Cloud Consumer B belongs to Department B.
During routine access of Cloud Service A by Cloud Service Consumer A, the Department A cloud resource administrator is notified that a hardware fault is occurring within Physical Server A that will soon cause it to fail. The cloud resource administrator scrambles to arrange for Cloud Service A to be relocated but is unable to do so before Physical Server A does fail. It takes several more hours of downtime until, with the cooperation of the cloud provider, the Cloud Service A implementation is successfully moved to Physical Server C and made live again. Managers at Department A demand that a system be put in place to avoid this scenario in the future.
Cloud Service A was initially developed specifically for Department A's Cloud Service Consumer A. However, recently Department B has indicated that it will be developing its own cloud service consumer that will also need to regularly access Cloud Service A. After this new cloud service consumer is deployed, both Department A and Department B experience occasional runtime errors when their cloud service consumers attempt to access Cloud Service A at the same time.
Cloud Service A accesses a legacy system on Virtual Server A that requires regular updates and patches to stay current. Each time the legacy system is updated, Cloud Service A needs to undergo an update as well, during which it needs to be temporarily unavailable. Department A managers ask the cloud provider to extend the cloud architecture so that a duplicate, secondary implementation of Cloud Service A can be made available while the primary implementation undergoes a maintenance update.
Which of the following statements provide a solution that can adequately resolve all of Departments A and B's issues?
Lynelle
6 months agoMatt
6 months agoRikki
6 months agoLaticia
6 months agoDenise
6 months agoKasandra
7 months agoLonna
7 months agoMarguerita
7 months agoWillard
7 months agoMendy
7 months agoRocco
7 months ago